Blockchain Basics
What is Blockchain?
Blockchain is a decentralized digital ledger that records transactions across a network of computers in a secure, transparent, and immutable way. Think of it as a shared Google Sheet that no single person controls – everyone has a copy, changes are agreed upon by the network, and once added, records can't be altered without consensus from the majority.
Key characteristics:
- Decentralized: No central authority; run by many computers (nodes)
- Immutable: Once data is added, it's extremely hard to change
- Transparent: Anyone can view the ledger (in public blockchains)
- Secure: Uses cryptography to protect data
- Consensus-driven: Nodes agree on the state of the ledger
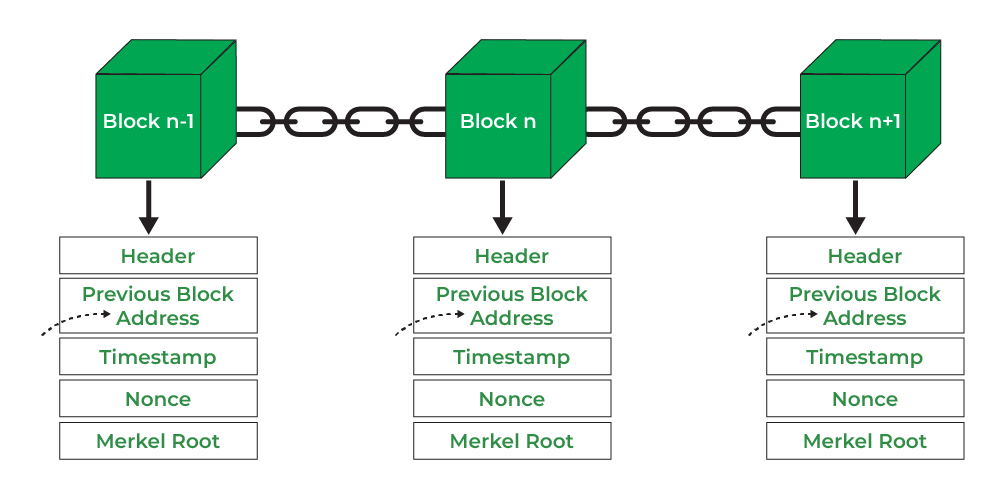
Blocks linked together like a chain, each referencing the previous one via hashes.
A Brief History of Blockchain
Blockchain ideas trace back to the 1970s–1990s with concepts like Merkle trees (1979) and secure timestamping (1991). The breakthrough came in 2008 when an anonymous person or group, Satoshi Nakamoto, published the Bitcoin whitepaper: "Bitcoin: A Peer-to-Peer Electronic Cash System." This introduced the first practical blockchain to enable trustless digital money.
Bitcoin launched in 2009 with the Genesis Block. Ethereum (2015) added smart contracts, expanding blockchain beyond currency. By 2026, blockchain powers cryptocurrencies, DeFi, supply chains, NFTs, and more, with ongoing improvements in scalability and energy efficiency.
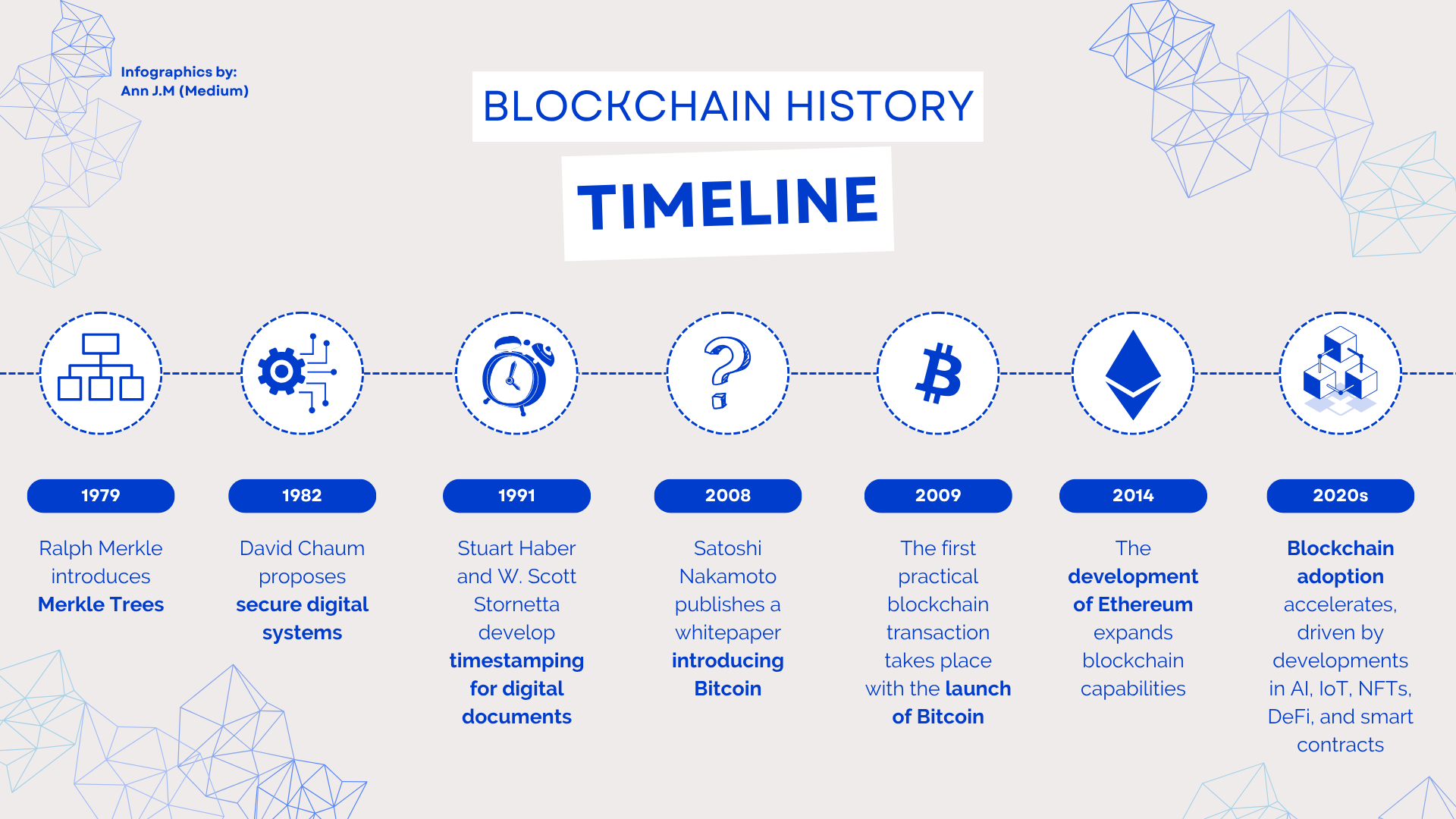
Timeline of blockchain evolution from early concepts to modern adoption.
How Blocks and Transactions Work
Blockchain organizes data into blocks, linked in a chain. Each block contains:
- Block Header: Metadata like previous block's hash, timestamp, nonce, Merkle root, difficulty target
- Block Body: List of transactions
Transactions are the core data – e.g., "Alice sends 1 BTC to Bob." They include sender/receiver addresses, amount, digital signature, and are broadcast to the network.
Process:
- User creates and signs a transaction
- Transaction enters the memory pool (mempool)
- Nodes validate it
- Miners/validators group valid transactions into a block
- Consensus (e.g., Proof-of-Work) secures the block
- Block added to chain; previous hash links it
- All nodes update their copy
The Merkle tree efficiently verifies transactions without storing everything.
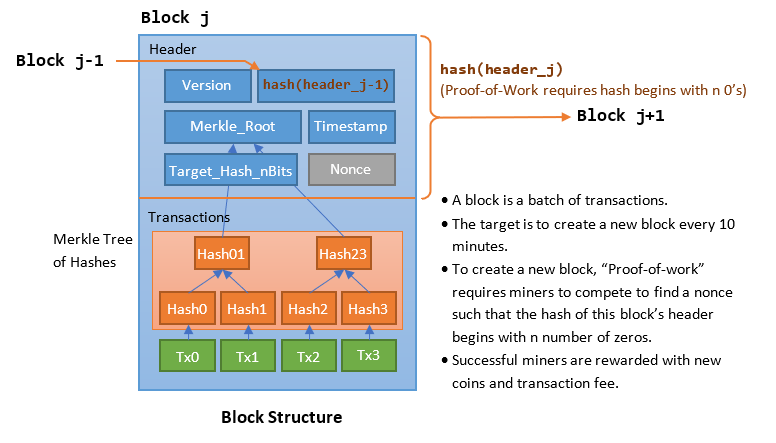
Bitcoin block structure showing header, Merkle root, and transactions.

Step-by-step: How a transaction becomes part of the blockchain.
Public vs Private Blockchains
Public blockchains (permissionless) are open: anyone can join, read, write (via consensus), and validate. Examples: Bitcoin, Ethereum. They prioritize decentralization, transparency, and censorship resistance but can be slower and more energy-intensive.
Private blockchains (permissioned) restrict access: only authorized participants join. Controlled by one organization or consortium. Examples: Hyperledger Fabric, Corda. They offer better speed, privacy, and scalability but less decentralization.
Hybrid and consortium variants exist for specific needs.
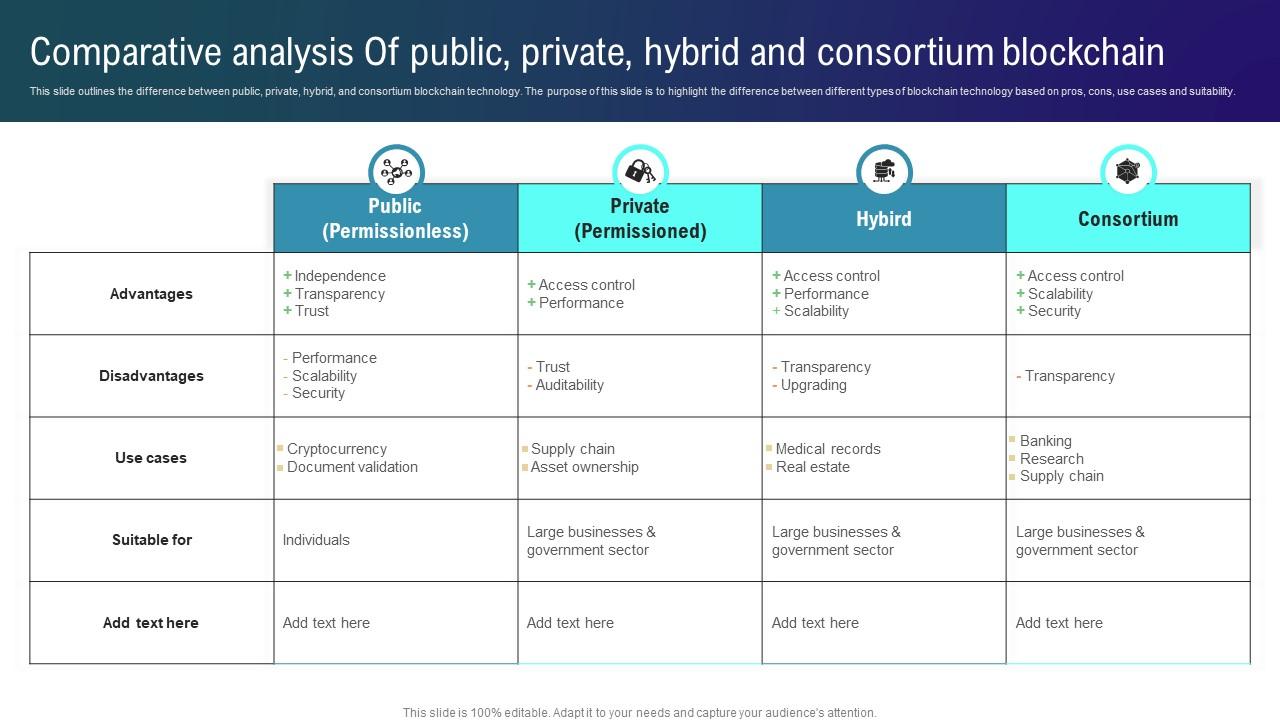
Comparison table of public, private, hybrid, and consortium blockchains.
Public Blockchain
Access: Open and permissionless. Anyone can join, read, and participate.
Control: Fully decentralized. No single entity has authority.
Transparency: Very high. All transactions are publicly verifiable.
Speed & Scalability: Generally slower and less scalable due to distributed consensus.
Security Model: Secured by cryptography and massive network participation (e.g., proof-of-work).
Primary Use Cases: Cryptocurrencies (Bitcoin), DeFi, NFTs, and public dApps.
Examples: Bitcoin, Ethereum, Solana.
Private Blockchain
Access: Permissioned and restricted. Participation is by invitation only.
Control: Centralized or controlled by a consortium of known organizations.
Transparency: Limited. Visibility is restricted to authorized participants.
Speed & Scalability: Faster and more scalable due to a smaller, trusted network.
Security Model: Secured through strict identity and access controls.
Primary Use Cases: Enterprise supply chain tracking, internal finance, and confidential healthcare records.
Examples: Hyperledger Fabric, R3 Corda, Quorum.
Complete this lesson
Mark as complete to track your progress